The Truth About Our WiFi Revealed: What the Profile Means for Privacy
What does our network do, how does it do it, and why does it do what it does?
April 26, 2017
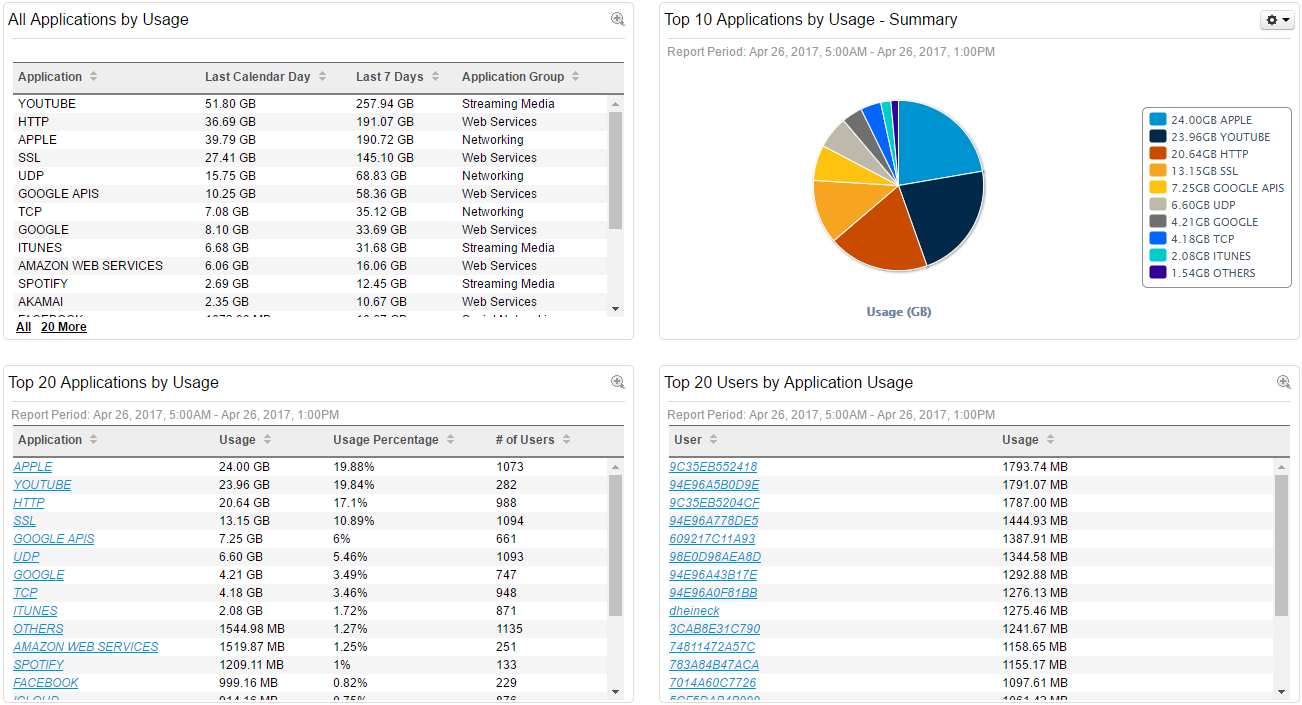
As I recently sat down with Mr. Heineck, our Director of Technology, in his high-tech library office while he showed me the basics of the school WiFi operations, we briefly came across an iPad named “Christine” on the database.
“Christine” had nearly 1.5 gigabytes (GB) of WiFi usage as monitored by our school-wide management platform, and just by looking at the ranking screen we could tell that this particular iPad had used the most WiFi data out of all the devices in the school for that day.
Like the owner of the “Christine” device, all students at La Salle rely on our iPads, and for the most part, we understand that our WiFi is a secured, controlled network. Blocked apps such as Netflix, Snapchat, Facebook, Instagram, Twitter, Tumblr, Hulu, and Steam remind us that at least in theory, our online endeavors are restricted to academic mode. However, most students actually don’t know all the potential capabilities of our WiFi system or even how our WiFi works; some students claim not to care, while others formulate strange stories of how the WiFi holds NSA-like surveillance capabilities, adding a sense of paranoia and confusion in regards to the school’s network.
In agreeing to sit down with me, I hoped Mr. Heineck could clear this confusion by answering our questions once and for all: what does our network do, how does it do it, and why does it do what it does.
“This is an exciting time in the history of education where we all have easy access to so much information and learning resources,” Mr. Heineck said. “In our iPads and smartphones, we all have more information than the Library of Alexandria and more computing power than the Apollo spacecraft that landed on the moon. At the same time, students and adults alike are challenged with how to use these resources consistently to our advantage.”
Essentially, the management profile installed at La Salle aims to help us do just that: create a powerful network environment that all students have equal and responsible access to. And after meeting with Mr. Heineck, it’s clear that the current management profile is, in fact, instrumental in enabling the wide-ranging Wi-Fi available at school, even if its covert abilities may unsettle some students.
But what exactly is the management profile?
The management profile is a database that allows access to La Salle’s secured network. We install the management profile to our devices, and this install acts as a registration key to the WiFi; Mr. Heineck explained, “When a device wants to connect to the WiFi network, the WiFi will send a message over to the database which basically asks ‘is this device, who’s requesting access to the network, registered in the database?’ and if it is registered in the database then the device is cleared, and if it is not a registration screen comes up”
Once installed, students grant access to the JSS “multiple device management platform”. And in turn, this platform has access to some information and certain functions on our iPads; functions that Mr. Heineck can execute right from his computer.
These are the commands that can be remotely applied to any iPad on the network:
- Have the iPad refresh itself in the database (in case of glitch or connection loss)
- Clear the iPad passcode
- Unmanage the device from the WiFi
- Wipe the device and reset to factory default
These commands can only be done while a student is connected to the school WiFi, not when the student is at home; while some students may interpret these as an overreach, the basis for these abilities is not entrapment or sabotage, but rather a precaution for troubleshooting devices more effectively. And because iPads are owned by students and not the school, these actions are actually lenient compared to schools who distribute iPads bought by the district: “All schools who use iPads use similar management systems,” Mr. Heineck told me, “but our system allows less access since devices are owned by families and not the school.”
But what surprised me the most was not the multiple commands the profile could administer. To me, the most sophisticated aspect of our Wi-Fi network is its processing, analyzing, monitoring, and safeguarding of information.
The WiFi itself is made possible through the 54 wireless access points stationed in strategic places around the school — Mr. Heineck monitors each one’s performance from his office, making sure none are experiencing or causing problems. From his office Mr. Heineck also monitors the flow of information through the Wi-Fi system; how the network and iPads are being used, how much network capacity is being used, and like our friend Christine found, he can tell who is using the most and follow up with them if need be.
“Between the MDM server and our Aerohive WiFi system, we can see what apps are installed on an iPad, but not the information and content stored in the app or the iPad,” Mr. Heineck described. “We can also see what websites are being accessed and how much data is being used, but not the particular content on the website. If needed, a particular device can be blocked from accessing school WiFi.”
Our internet is a shared network, which means that if a student or group of students is using up all the bandwidth it affects everyone in the school. For instance, if “Christine” is downloading 13 applications onto her iPad while watching YouTube in the library, then students in actual classes will most likely experience delays. This is why Mr. Heineck insists that monitoring school web traffic is a necessary precaution; the internet must be equally available.
The network provides basic statistics on what kind of traffic is being sent in certain categories, such as the 20 most used apps or the gigabyte amount of web traffic, for the roughly 1000 devices that log on daily. It can see if some people are using too much bandwidth (usage exceeding 10 GB may prompt Mr. Heineck to follow up with the given student) and ranks students accordingly.
Though the profile can identify basic website info on devices, the management profile does not have the ability to track specific website activity or app activity, and can only track this basic website info while on the school network. For example, the profile can’t specifically survey or recognize that a student is on Google Slides or Google Docs, but it will indeed recognize and register on Mr. Heineck’s computer that the student is using a Google application programming interface (API), the general online software allowing Google services to communicate with the user.
And again, when you are at home and not on the school WiFi, the profile installed has no power whatsoever.
Mr. Heineck believes that “La Salle has a responsibility and obligation to have the ability to monitor and restrict web traffic to help provide a positive and productive learning environment.” The profile helps La Salle fulfill this responsibility.
Furthermore, tracking website data helps Mr. Heineck decide how to most effectively configure the network itself: “With this knowledge, [tracking] helps us design the network and the classrooms so that WiFi performs as well as possible” Heineck argues.
After finally learning how the WiFi I had grown accustomed to actually operated, I still had one question remaining. How does La Salle decide what gets blocked and what gets monitored? As our meeting came to a close, I wondered if the advanced machinery, technology oriented learning and sophisticated network processes were all complicated solutions to a complicated age of the internet.
But for our Director of Technology, technology is a bit more simple.
“We generally follow the guideline of whether a particular app helps build a positive and productive learning environment. Does a particular app serve learning and students’ best interests while they’re on campus?” If not, the school has it in their power to determine if an app should be blocked; for websites, we subscribe to a web content filtering service that blocks “harmful or objectionable content” in accordance with Federal CIPA law.
I was surprised by his transparency. If La Salle was using the profile as a way to spy on or administer strict regulation on us students, it wasn’t evident when I witnessed its interface.
But for those who still feel doubt, Mr. Heineck’s door is always open:
“If any students are interested, I’m happy to show how our WiFi network and management system works.”
***
What questions do you have about the WiFi system and the device management profile? Let us know in the comments below, and we’ll do our best to provide an answer.




Coleman • Apr 27, 2017 at 9:56 am
Shak, great article! I appreciate you taking the time to do the research, ask the right questions, and educate us about the school’s network and students’ profiles. Thank you!
Liz • Apr 26, 2017 at 9:49 pm
Nice work, Shak! I know this topic has been a buzz around campus. You did a nice job clarifying many questions and concerns that have been voiced by our student body.
John • Apr 26, 2017 at 9:16 pm
Very interesting topic, Shak. I think this is something that most people want to know, but just don’t have to initiative to find out.